
Ambition Driven Bright Ideas
The Insatiable Hunger to Build Projects
According to Tim Cook of Apple fame, the key difference between pretty good workers and the brilliant ones, the top performers want to impact other people or the world around them.
tl;dr
- Talking about Code dismisses Lore to Build Knowledge
- Found a Home in the Field of Data Cryptography
- Address the Root Cause, Not the Symptoms, Build for Maintainability
- Consider the Flow of Data and the Impact it Brings
- From Interactive on Screen User Experiences to Protocols That Make Services Come to Life
- Well Engineered Software is its Own Heaven, Poorly Engineered Software is its Own Hell
Safe Network Sharing Does Exist
Public Key Infrastructure is the mathematically proven technology to keep data safe from prying eyes and proving authenticity against phishing scams. This now requires considerations of the flow of data within and across devices and organizations and the network protocols the flow travels. It's complex to enter but was done! The outcome is protocols used amongst processed that live in different security sandboxes. System processes that require security credentials but not hard coding those instead communicate with the proper end user services with security keys and credentials protected. If that’s not enough orchestrate in event driven multi-threaded operations that also sync with IO.
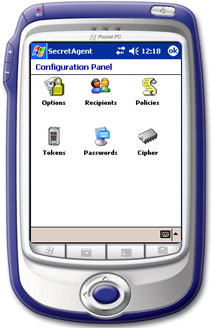
For people forward design the choice was clear to use integration with the Operating System shell. It’s the most fluid way into the various containers of encryption strength and digital signature integrity. It's the details of the how where lies the passion.
Sniff Out The Discipline - The story behind the philosophy
The Best Windows OS That Never Was
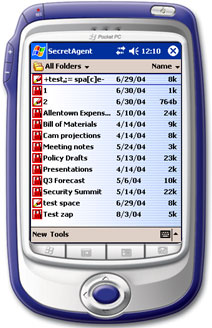
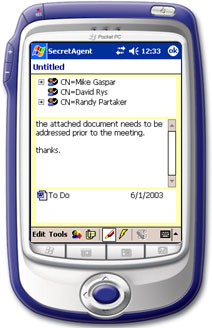
The problem with a mathematically secure way to keep content that lives on and soars across our technology is ease of use. A client request to have files archives containing sensitive information go from desktop to PDA presented a challenge: A simple tap to decrypt, view, edit and re-encrypt automatically. The automation of what was prior a manual operation was honorably dubbed the Gaspar New Paradigm. This technology is long gone but the memory remains.
Graduating to Something More
Finding a home in the field of data cryptography isn’t the origin of the story nor is it the destination. That story is set at the campuses of DePaul University for not one but two degrees. Here is where the journey veers deep in the trenches with C++ to implement the disciplines of Distributed Systems. That is the complexities in making systems communicate with each other. Skilled in the use of the well-respected framework of Qt and armed with vast knowledge to prototyping distributed event driven applications began.
Qt Skillz FTW! - a fun C++ and Qt project
The All New SpyProof!

This product was born out of the need to protect intellectual and sensitive private data. Modeled to mitigate the massive losses of trade secrets, future products and Human Resource information about all the employees in a major gaming Studio that occurred from a ransomware attack! When all other security measures have been breached stolen data is rendered as worthless gibberish when viewed outside its owners infrastructure.
How Cybersecurity Is Simplified - Dig Deeper about Engineering SpyProof!Build to Create; Remaster to Reboot
Imagine a lake side beach town where main street is lined with small business, pizza and wine are enjoyed on roof top restaurants and everyone knows the downtown theater is haunted. What can shopping for records in the dimly lit record store of a basement do to motivate the next projects? Serve as the reminder that putting people first when sharing passion can build an amazing community. The next big vision is to harness the power of data security first design combined with disciplines of distributed systems and bring this to the home lab and creation communities. Never stop building! Especially if it is for yourself.

Refactoring from Syntax Error to Hello World
Behind every great developer is a long list of errors they didn't give up on. Every bug, crash, and exclaimation of "Why isn't this working?" isn't a failure, just all part of the process. The append-only log of tracking the path through the wilderness of technical debt awaits. There exists love to share insightful blogs about the field and challenges that can be avoided going forward.
Keep coding, keep breaking things, keep fixing them! We welcome you to immerse yourself in the lunar lunacy! The Append-only blogs are updated along with post by SagaveWolffy on Linked In and Bluesky. No need to wait for the next full moon!
Append Only (Coming Soon) - about software system creation
The corporation versus studio battle heats up. No one likes corporate life, no one wants to be part of corporate life. This is what can be done when a University Background, an Imaginitive mind and the awesomeness of the home lab combine.
Coming Onshore - Dig Deeper about The Reboot